Food Fraud Vulnerability Assessment: A Complete Guide for Food Manufacturers
.avif)
Food fraud cases surged 10% in 2024, and industry analysts project the same rate of increase through 2025. Geopolitical disruptions, ingredient price spikes, and increasingly opaque supply chains are all contributing factors. When economic pressure rises, the incentive for suppliers to cut corners rises with it: substituting cheaper ingredients, diluting concentrates, or mislabeling origins.
Every major GFSI certification scheme now requires a documented food fraud vulnerability assessment (FFVA). FSMA-regulated facilities handling imported ingredients carry additional supply chain program obligations under 21 CFR Part 117. And yet many quality teams are still working from outdated spreadsheets or assessments that were completed once and never revisited.
This guide walks through exactly how to conduct an FFVA that satisfies both FSMA and your GFSI certification requirements, including what to do with the output once the assessment is complete. Scoring tables, mitigation frameworks, and audit-readiness checklists are all embedded here so you can reference them without hunting for separate downloads.
What Is a Food Fraud Vulnerability Assessment?
Definition
A food fraud vulnerability assessment is a documented, risk-based procedure that identifies which ingredients, materials, or products in your supply chain are vulnerable to economically motivated adulteration or substitution. It scores the likelihood and potential impact of each vulnerability to produce a risk-ranked register.
The key word is intentional. An FFVA addresses deliberate acts by economically motivated actors in your supply chain, not accidental contamination events. This separates it from your HACCP hazard analysis, which focuses on unintentional physical, chemical, and biological hazards. Your HACCP plan and your FFVA work in parallel, but they answer different questions.
The FDA uses the term "economically motivated adulteration" (EMA) to describe the specific threat your FFVA addresses. The agency defines EMA as the fraudulent, intentional substitution or addition of a substance in a product for economic gain. You can review the FDA's EMA guidance for the full regulatory definition and enforcement context.
VACCP, FFVA, and TACCP: What's the Difference?
These three terms are used inconsistently across the food safety industry, and the confusion causes real problems when facilities try to build compliant programs. Here is the precise distinction:
VACCP (Vulnerability Assessment and Critical Control Points) is the GFSI-endorsed framework for assessing food fraud risk. It is the food fraud parallel to HACCP: a structured, documented approach to identifying and controlling intentional economic adulteration threats in your supply chain.
FFVA (Food Fraud Vulnerability Assessment) is the documented output of the VACCP process. When someone says your facility needs an FFVA, they mean you need to complete and maintain the assessment record that VACCP methodology produces.
TACCP (Threat Assessment and Critical Control Points) addresses a completely different problem: malicious tampering or contamination by a bad actor intending to cause harm. TACCP is the food defense framework. FSMA addresses TACCP threats under 21 CFR Part 121 (the Intentional Adulteration Rule), which is entirely separate from the supply chain program requirements under Part 117.
A useful way to think about it: VACCP is about profit motive, TACCP is about malicious intent. Both are required under GFSI certification, but they are managed as separate documented programs.
When it comes to FSMA, the agency calls the equivalent obligation a "supply chain program" rather than VACCP or FFVA. The underlying methodology is equivalent: you are identifying hazards controlled by your suppliers and establishing controls for them. If you are completing an FFVA to satisfy your GFSI scheme, that same documented assessment satisfies the FSMA supply chain program requirement for EMA hazards.
What Counts as Food Fraud?
Food fraud covers a range of deliberate practices, all motivated by economic gain. The six recognized fraud types are:
- Substitution: replacing an authentic ingredient with a cheaper alternative (e.g., substituting a lower-grade fish species for a premium one)
- Dilution: extending a genuine ingredient with a cheaper substance while retaining the original label (e.g., honey extended with corn syrup)
- Addition: adding an undeclared substance to improve apparent quality metrics (e.g., adding melamine to milk powder to inflate protein readings)
- Concealment: hiding inferior quality within a product (e.g., blending spoiled product with fresh to meet spec)
- Mislabeling: false or misleading declarations on origin, grade, or species
- Counterfeit: producing an entirely fake product designed to look genuine
Your FFVA must consider all six types for each ingredient in scope. The GFSI Technical Document on Food Fraud provides a detailed breakdown of how each fraud type maps to specific commodity categories.
Is a Food Fraud Vulnerability Assessment Required?
GFSI Requirement (All GFSI-Certified Facilities)
GFSI Version 7.2, issued in 2018, mandated food fraud vulnerability assessment across all GFSI-benchmarked certification schemes. If your facility holds or is seeking SQF, BRCGS, FSSC 22000, or any other GFSI-recognized certification, a documented FFVA is a non-negotiable requirement, not a best practice.
This requirement applies whether your facility handles high-risk commodities or relatively stable ones. Every ingredient and material in scope must be assessed. Incomplete coverage is one of the most common non-conformances auditors flag. Your food safety management system must include FFVA as a documented, maintained component, not a one-time exercise.
FSMA Supply Chain Program Obligations
Under 21 CFR Part 117 Subpart G, US food manufacturers must implement supply chain programs for any hazard controlled at the supplier level. Economically motivated adulteration is an explicit example of a supply chain hazard that FDA expects facilities to address in their hazard analysis.
Your PCQI (Preventive Controls Qualified Individual) must review and approve the supply chain program. If you have PCQI training on your team, your FFVA should be incorporated into the supply chain program section of your food safety plan as documentation of how EMA hazards have been evaluated. The FSMA 204 traceability requirements operate in the same regulatory landscape and reinforce why supply chain visibility matters at every tier.
FSMA does not use the term FFVA, but the substance of what it requires for EMA hazards maps directly to what GFSI schemes call an FFVA. Completing one rigorous assessment that satisfies GFSI clause requirements will generally satisfy the FSMA supply chain program documentation standard for EMA as well.
Compliance Table: FFVA Requirements by Scheme
No competitor provides a side-by-side breakdown of how FFVA requirements differ at the clause level across FSMA and the major GFSI schemes. This table is the reference.
For FSSC 22000 V6 specifics, the FSSC 22000 Food Fraud Mitigation Guidance document provides clause-by-clause implementation guidance. For BRCGS Issue 9, the BRCGS Vulnerability Assessment for Food Fraud resource covers the scheme's specific expectations.
How to Conduct a Food Fraud Vulnerability Assessment (Step-by-Step)
Step 1: Compile Your Ingredient and Material Register
Your FFVA starts with a complete inventory of everything in scope. Pull every raw material, ingredient, processing aid, and packaging material from your approved supplier list and bill-of-materials documentation.
Group items by commodity category for efficiency: proteins, oils and fats, grains, spices and flavorings, sweeteners, seafood, dairy, botanicals, and packaging. Grouping does not mean you score the whole category together. Each distinct ingredient still needs its own assessment record. Grouping just makes the workflow manageable and ensures you do not miss entire commodity areas.
Your supplier management software should be your primary data source here. If your approved supplier list and ingredient register are maintained separately, reconcile them before you start scoring. Discrepancies between your supplier list and your FFVA scope are exactly the kind of coverage gap auditors flag.
Step 2: Identify Historical Fraud Incidents and Alerts
Before you score any ingredient, research its fraud history. Prior incidents dramatically increase the likelihood score for that commodity. "I wasn't aware of the incident history" is not an acceptable audit response.
Your research sources should include:
- FDA EMA enforcement actions and import alerts: search by commodity on FDA's website for current enforcement activity
- EU RASFF (Rapid Alert System for Food and Feed): covers European fraud incidents and alerts for products entering EU markets; accessible via the RASFF portal
- USP Food Fraud Database: the USP Food Fraud Mitigation Guidance and accompanying database catalog documented incidents by commodity, making it a practical starting point for likelihood research
- Industry publications and trade associations: FoodNavigator, Food Chemical News, and commodity-specific trade groups regularly report fraud incidents
Document your research sources in your FFVA record. Auditors want to see that your likelihood scores are evidence-based, not guesses.
Step 3: Score Vulnerability (Likelihood × Consequence)
The standard FFVA scoring model uses two axes: likelihood of fraud occurring and consequence if it does. Multiplying the two scores produces an overall vulnerability rating for each ingredient.
This scoring framework is embedded below. Use it directly in your assessment.
Likelihood Scoring
Score each factor on its 1–5 scale, then average the factor scores to produce the overall Likelihood score (1–5).
Consequence Scoring
Score each factor on its 1–5 scale, then average for an overall Consequence score (1–5).
Overall Vulnerability Score = Likelihood Score × Consequence Score
Document your own thresholds and the rationale for them. The ranges above are a widely used starting point, consistent with the methodology in the Food Fraud Prevention Think Tank FFVA Primer. If your scheme auditor or internal risk policy uses different thresholds, align to those and document the decision. For academic grounding on the methodology, the 2020 peer-reviewed study on FFVA methodology in Food Research International provides a thorough review of scoring approaches across global frameworks.
Step 4: Determine Which Vulnerabilities Are Significant
A vulnerability is significant when two conditions are both true: the overall score meets or exceeds your high-risk threshold, and no current control adequately mitigates it.
The second condition matters. If you already have robust analytical testing and a third-party audit program for a high-scoring ingredient, you may be able to document those controls and reclassify the residual risk as medium or low. What you cannot do is score an ingredient as high-risk and then take no action. SQF, BRCGS, and FSSC 22000 all explicitly require a written mitigation plan for every ingredient you classify as a significant vulnerability.
Write out your significance determination in plain language for each ingredient reviewed. Auditors will ask to see the rationale. A numeric score with no narrative explanation is rarely sufficient.
Step 5: Write Your Mitigation Plan
Once you have identified significant vulnerabilities, you need a documented mitigation plan for each one. The next section covers how to build that plan in detail.
Before you get there: document the link between your FFVA output and your mitigation plan clearly. Auditors look for a traceable connection between the vulnerability record and the control measures put in place. If they are in separate documents, cross-reference them. If they are in the same document, structure it so the relationship is obvious. Maintaining this connection is also important when preparing for your food safety audit.
Step 6: Review and Update the FFVA
All three major GFSI schemes require at least an annual FFVA review. "Annual" means a documented review with a date, reviewer name, and a recorded outcome. A note that the document was not changed does not satisfy this requirement.
Beyond the annual cycle, specific trigger events require an unscheduled review:
- A new ingredient or raw material is added to your register
- You change a supplier for an existing ingredient
- A commodity price spike creates new economic incentives for fraud
- A new fraud alert is issued by FDA, RASFF, or a trade body for a commodity you use
- A supplier audit produces a failure or significant finding
- Your GFSI certification scheme releases an updated standard with new FFVA requirements
Document the date, reviewer, trigger (annual or event-driven), and outcome of every review cycle. A gap in review history is one of the most common FFVA non-conformances at audit.
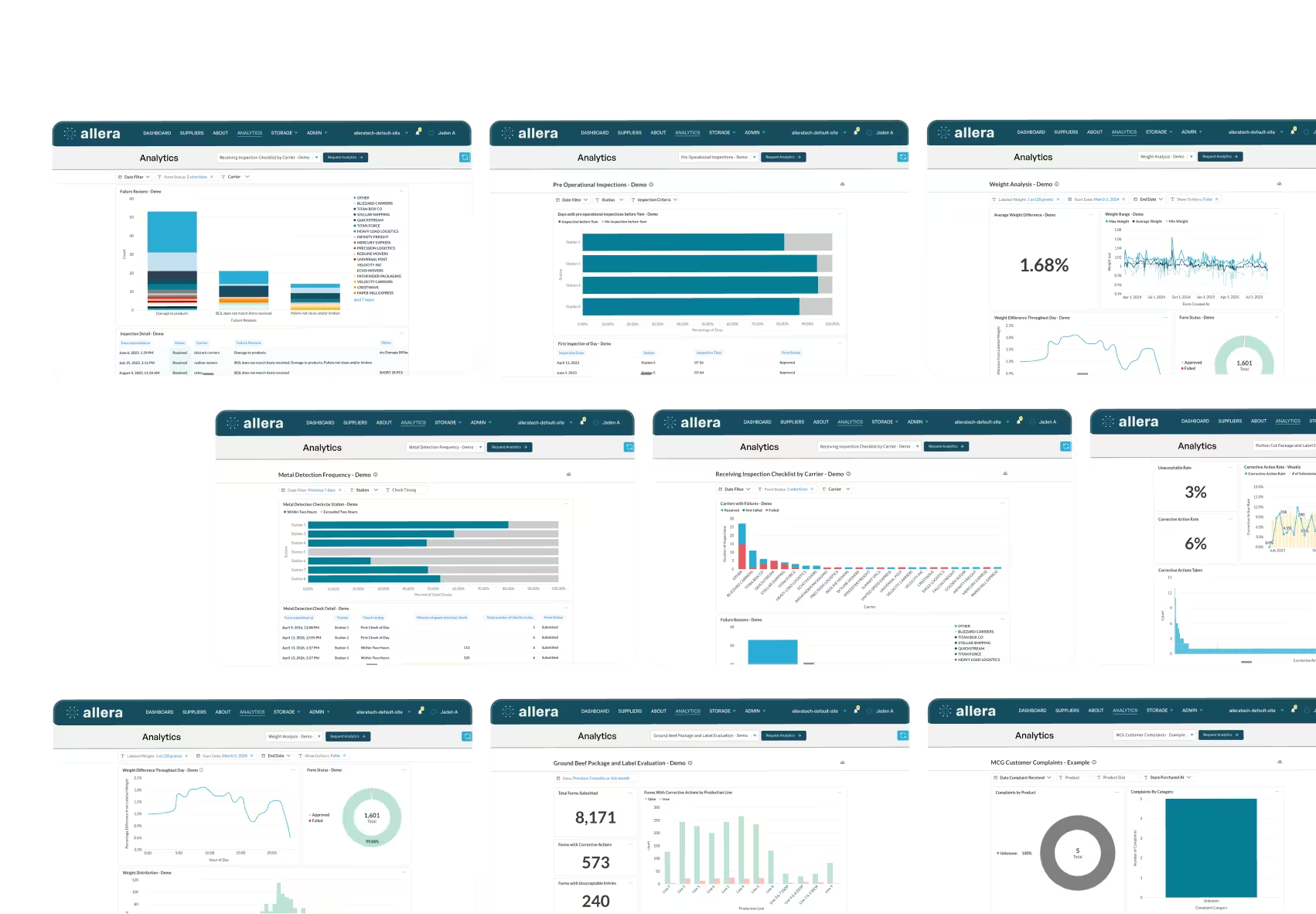
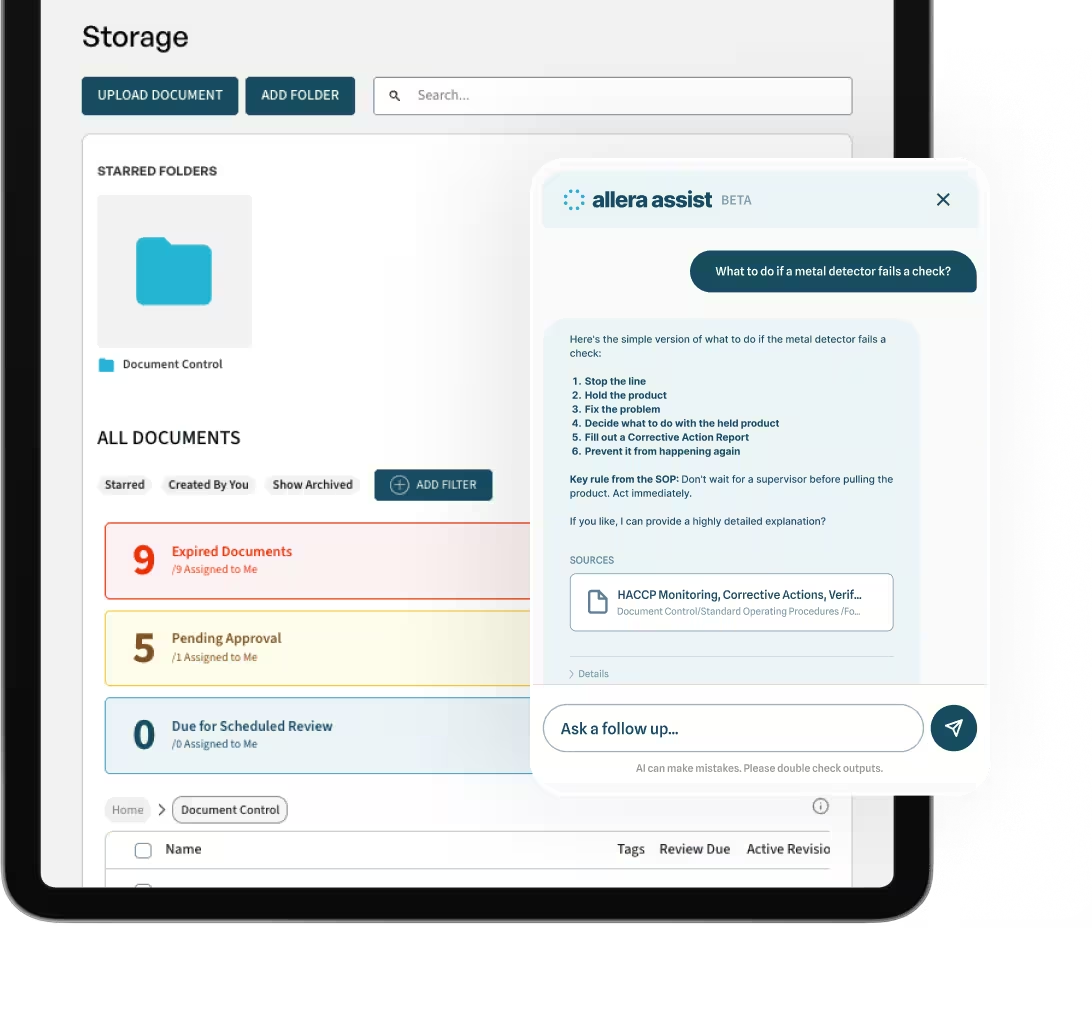
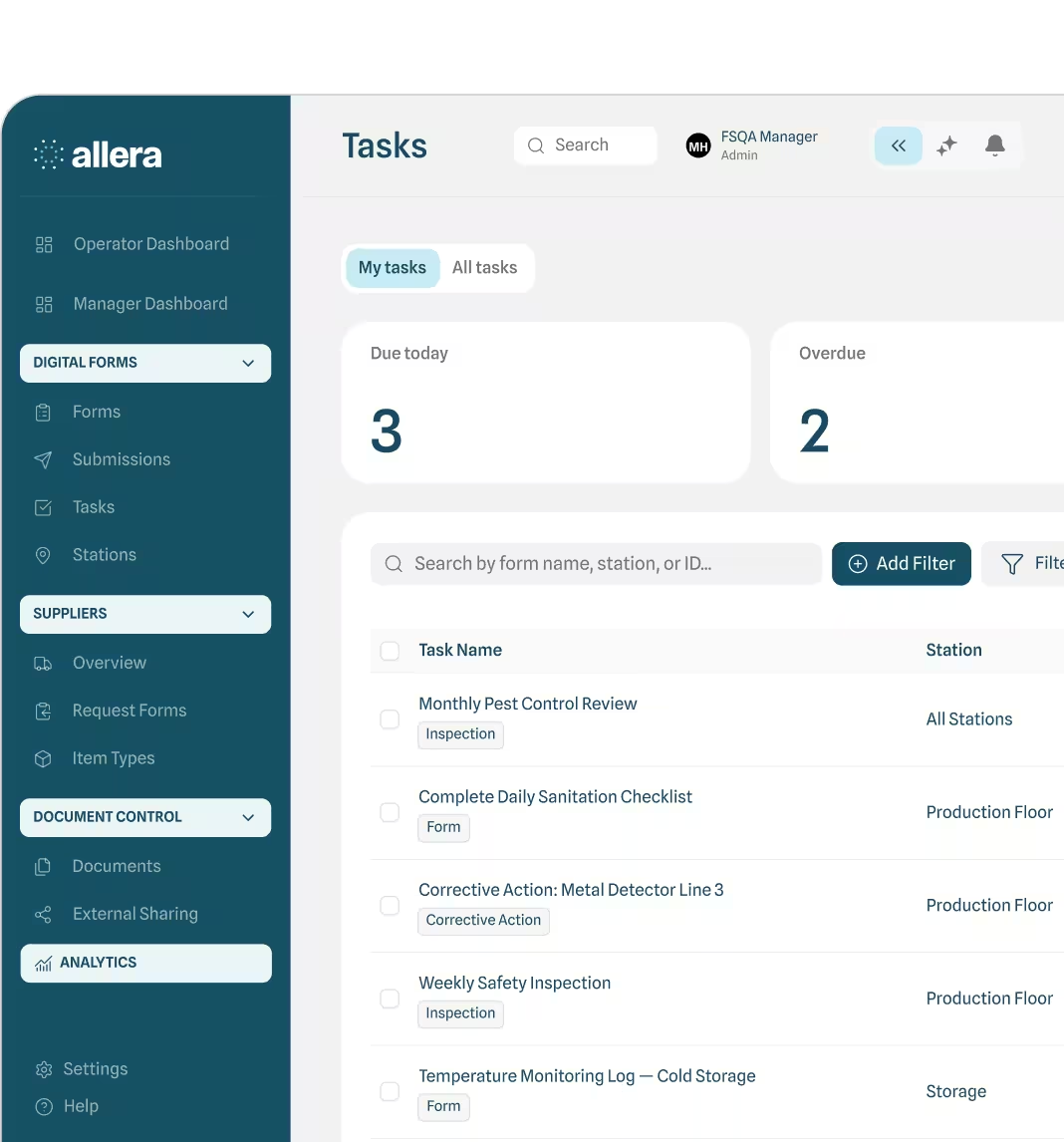
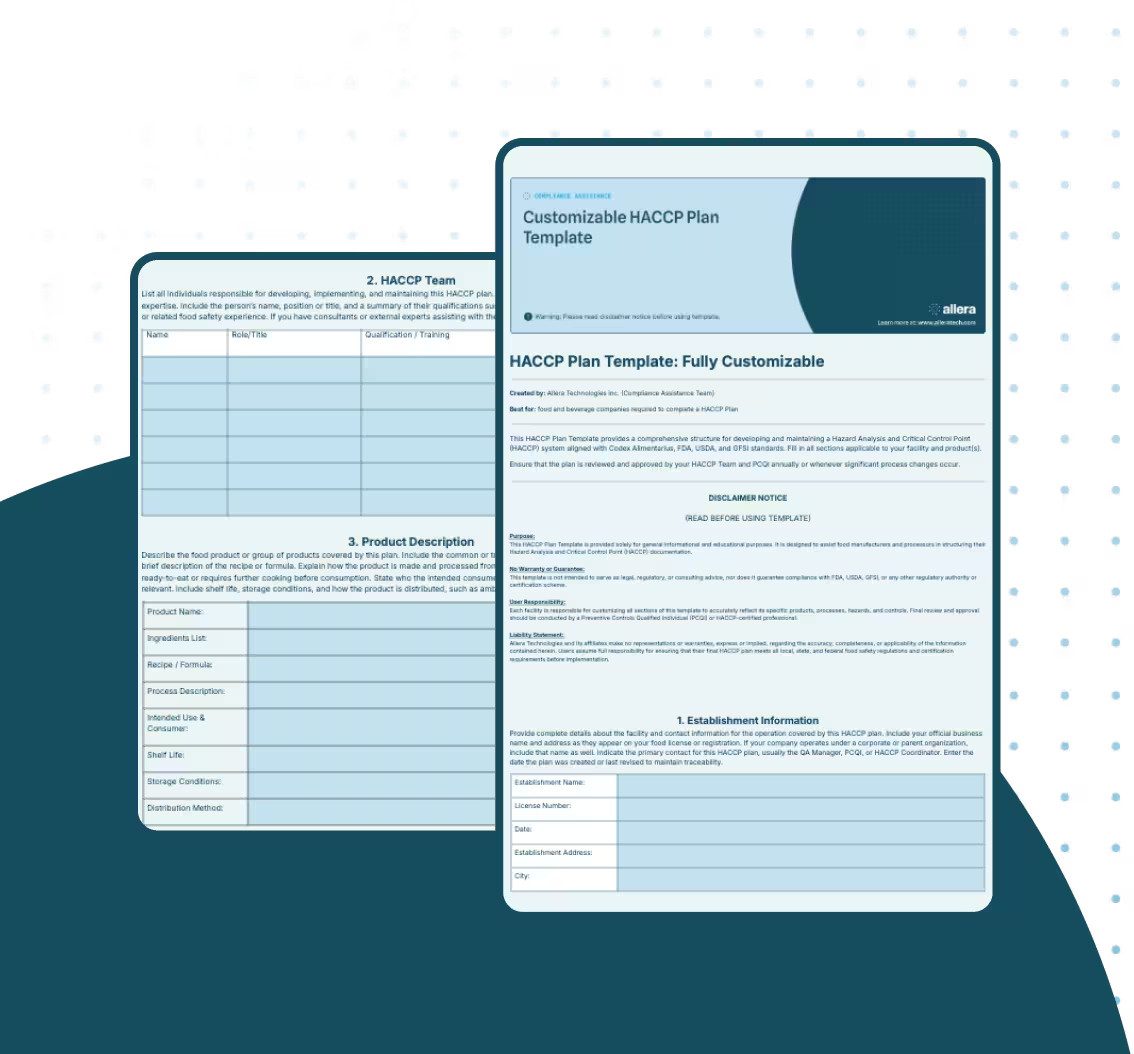
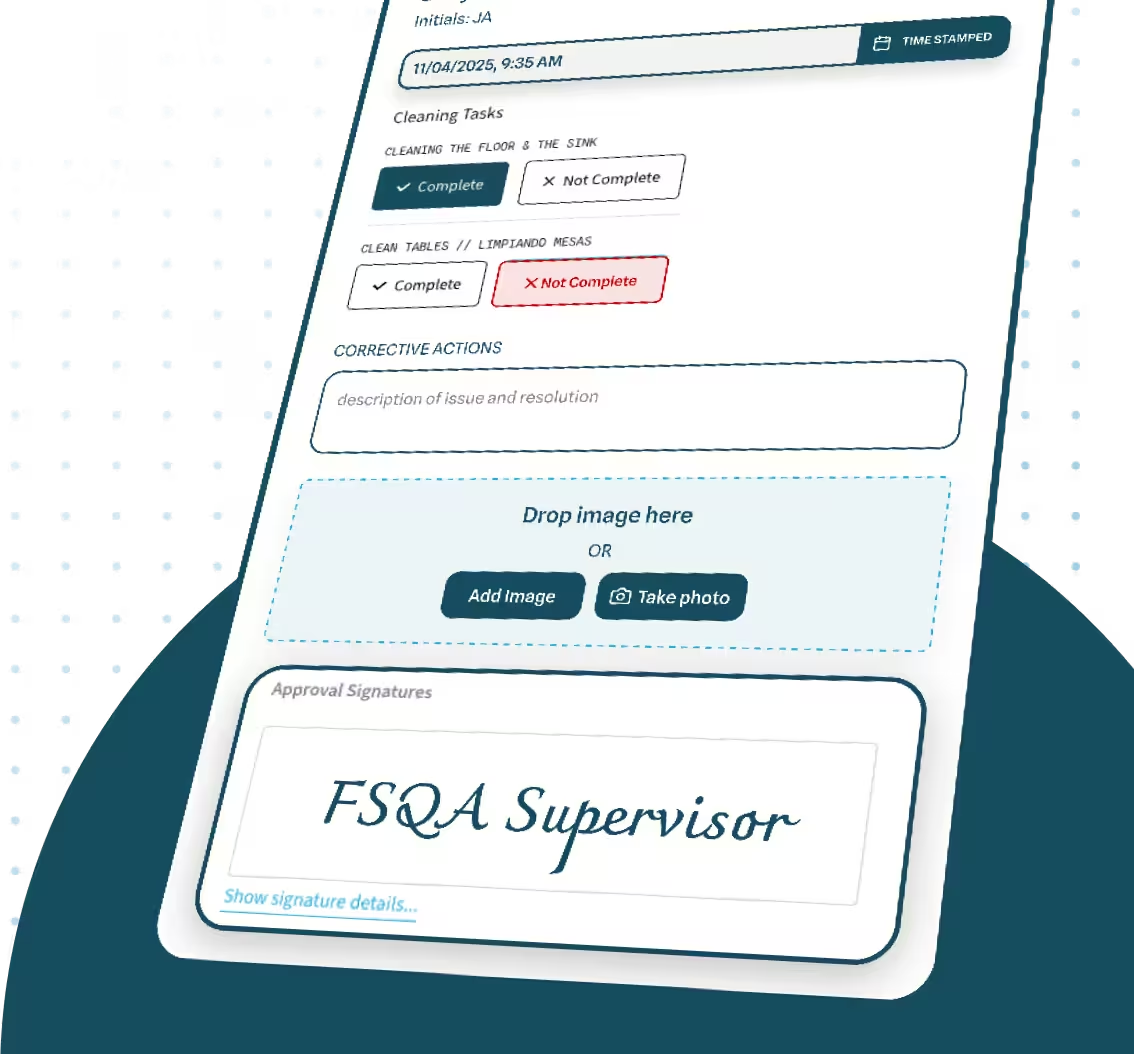
Managing FFVA records across multiple suppliers and certification cycles in spreadsheets creates gaps auditors find immediately. Allera lets food manufacturers document vulnerability scores, track mitigation status, and retrieve full FFVA history for SQF, BRCGS, and FSSC audits in one place. See How It Works
High-Risk Ingredients for Food Fraud
FDA's EMA surveillance program and the EU RASFF database consistently flag the same commodity categories year after year. Use this table as your starting point when prioritizing which ingredients to score first and which warrant extra scrutiny during Step 2 research.
This is a prioritization reference, not a complete risk register. Every ingredient in your operation must still go through the full scoring methodology. High-risk commodities just deserve extra thoroughness during the likelihood research phase.
If you source any of these commodities, treat them as likely candidates for a significant vulnerability score and plan your mitigation accordingly. If your sourcing currently runs through multiple intermediaries for any of them, your likelihood score will be high almost by definition.
How to Build a Food Fraud Mitigation Plan
What the Mitigation Plan Must Include
For each ingredient your FFVA classifies as a significant vulnerability, your mitigation plan must document six things:
- The specific ingredient or material
- The fraud type identified as significant
- The mitigation measure or measures selected
- The person responsible for each measure
- The monitoring frequency and method
- The corrective action procedure if a measure fails or monitoring shows a breach
Auditors review mitigation plans against the FFVA output directly. If an ingredient is listed as a significant vulnerability in your FFVA with no corresponding entry in your mitigation plan, that is a non-conformance. The connection between the two documents must be traceable.
Your food safety management system should house both documents in a way that makes this connection explicit, whether through cross-references, a combined document structure, or a management platform that links vulnerability records to control measures.
Mitigation Strategies by Vulnerability Type
Not all significant vulnerabilities call for the same response. The right mitigation strategy depends on why the ingredient scored as significant. Use this table to match your vulnerability type to the most appropriate control measures.
You do not need to implement every strategy in the table for a single ingredient. Document the measures you select, explain why they are sufficient to reduce the risk to an acceptable level, and assign a named owner to each. That is what auditors look for.
A few mitigation strategies deserve consistent use regardless of specific vulnerability type:
- Approved supplier program: your first line of defense; every ingredient should come from a qualified, documented supplier. This is also a core function of your food traceability program.
- Supply chain transparency requirements: building origin documentation into supplier agreements reduces your food and beverage supply chain risk from the procurement stage.
- Analytical testing: for high-risk commodities where visual or documentation checks are insufficient, scheduled analytical testing is the most defensible mitigation measure you can implement.
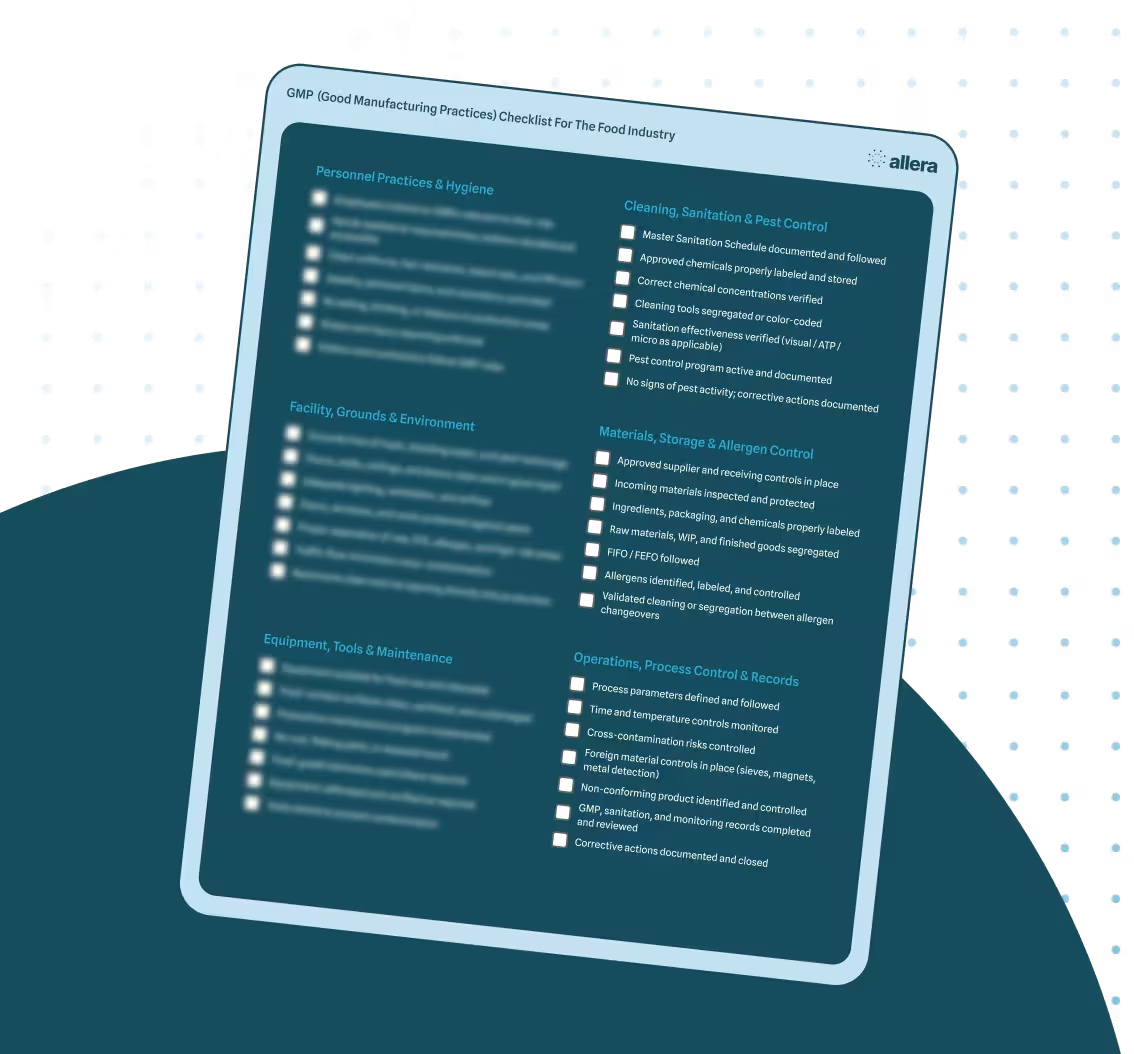
- Good Manufacturing Practices baseline: your Good Manufacturing Practices program establishes the baseline controls that fraud mitigation builds on. Facilities with strong GMP programs have fewer vulnerabilities from concealment and addition fraud types.
Integrating the Mitigation Plan Into Your FSMS
A mitigation plan that exists only on paper is not a functioning control. The measures you specify must actually be implemented, with monitoring outcomes recorded against them.
Assign each measure to a named owner (not just a department) and a due date for implementation if it is not already in place. Record the outputs of monitoring activities (COA reviews, audit results, testing results) in a form that links them back to the specific FFVA vulnerability they address. Internal audit your FFVA and mitigation plan at least annually as part of your FSMS internal audit cycle.
For FSSC 22000 Version 6 facilities, there is an explicit performance evaluation requirement. Under ISO 22000 Clause 9, you must evaluate the effectiveness of your mitigation plan, not just implement it. Document what metrics you use to evaluate performance, how often you evaluate, and what the evaluation results show.
Food Fraud vs. Food Defense: The Critical Distinction
The FDA's position 3 result for "food fraud vulnerability assessment" actually covers food defense, not food fraud. Many facilities conflate the two programs, which creates compliance gaps in both directions.
Both programs are required for GFSI-certified facilities. They are maintained as separate documented programs with distinct scope, methodology, and output documents. They do share underlying data sources: your supplier list, facility risk mapping, and ingredient register feed into both. The programs answer different questions and are audited separately.
If you are working from a single combined document that tries to cover both, you are likely creating coverage gaps in both programs. Separate them. Your food safety plan should reference both programs with clear delineation of scope.
How to Prepare Your FFVA for a GFSI Audit
What SQF Auditors Look For (Edition 9)
SQF Edition 9 Clause 2.6.2 requires a documented FFVA that covers all raw materials in scope, not a selected subset. Coverage gaps are the most common finding. Our complete guide to SQF certification covers the full scope of what auditors review, but the FFVA is consistently one of the first records pulled.
Before your audit, verify that your FFVA record:
- Is documented within your food safety management system and version-controlled
- Covers every raw material and ingredient on your approved supplier list, with no omissions
- Includes a mitigation plan entry for every ingredient scored as a significant vulnerability
- Shows at least one annual review with a documented date, reviewer name, and outcome
- Is linked to your supplier qualification records
Your SQF audit checklist covers the broader audit requirements. Have the FFVA record staged and accessible before the opening meeting.
What BRCGS Auditors Look For (Issue 9)
BRCGS Issue 9 Clause 5.4.1 requires the FFVA to be reviewed annually or whenever there is a significant change in raw materials, supply chain, or market conditions.
BRCGS also expects VACCP awareness at senior management level, not just in the QA team. This means senior leaders need to be briefed on the FFVA findings and sign off on the mitigation plan. Document that sign-off. Auditors for BRCGS certification sometimes ask management representatives directly about FFVA findings during facility tours or opening meetings.
Your mitigation plan can be a standalone document or integrated into your FFVA record. BRCGS accepts either format as long as the linkage between vulnerability findings and control measures is clear.
What FSSC 22000 Auditors Look For (V6)
FSSC 22000 V6 adds a documentation requirement that SQF and BRCGS do not explicitly call out: you need a documented procedure for conducting the FFVA, not just the assessment record itself.
The procedure should describe how you identify scope, how you research fraud history, how you score likelihood and consequence, how you determine significance, and how you trigger reviews. Auditors will sample-check your assessment records against your procedure to verify that the documented methodology was actually followed.
The FSSC 22000 Food Fraud Mitigation Guidance V6 document is the authoritative reference here. For more on what V6 changed and how it affects your FSMS, see the FSSC 22000 Version 6 overview.
Records to Have Ready Before Your Audit
Regardless of which scheme you are being audited against, have these records staged and accessible:
- Current FFVA document: dated, version-controlled, signed by the responsible owner, showing all ingredients assessed with their scores and significance determination
- Mitigation plan: with the current status of each measure (open, in-progress, closed) and evidence of implementation for closed measures
- Annual review record: meeting notes, updated risk scores, or a formal review document showing the date, participants, and outcome of the most recent review
- Corrective action records: for any monitoring failures or supplier non-conformances that triggered a mitigation plan response
- Supplier qualification records: showing that suppliers for significant-vulnerability ingredients have been assessed and approved
Your food quality management software should make retrieving this package straightforward. If you are currently managing these records across separate spreadsheets and shared drives, audit preparation will require significant time to reconstruct the paper trail. That reconstruction risk is itself a reason to consolidate.
Free Tools and Resources for Your FFVA
SSAFE Free Vulnerability Assessment Tool
The SSAFE tool was developed in partnership with PwC and Wageningen University and is available in 10 languages. It covers assessment at the ingredient, site, and company level and is the most widely referenced free FFVA tool in global food safety programs. It is designed as a structured Excel workbook. Visit the SSAFE Food Fraud Vulnerability Assessment Tool page to download it directly.
USP Food Fraud Database
The USP maintains a searchable database of food fraud incidents by commodity, updated on an ongoing basis. It is the most practical starting point for Step 2 of the methodology: historical incident research. The USP Food Fraud Mitigation Guidance document accompanies the database and provides commodity-level fraud characterization.
FDA EMA Surveillance Data
FDA publishes the results of its EMA surveillance sampling programs by commodity. Current published programs cover honey and seafood with specific sampling data. Use FDA's published import alert database alongside EMA surveillance results to identify current enforcement priorities for commodities you source. The FDA EMA guidance and data page is the central access point.
GFSI Technical Document on Food Fraud
The GFSI Technical Document provides detailed guidance on how VACCP and TACCP integrate into food safety management systems across all GFSI-benchmarked schemes. It is an essential reference if you are maintaining FFVA compliance across multiple certifications or if your team is building an FFVA program from scratch. The GFSI Food Fraud Technical Document is available for free download from the GFSI website.
FAQs
%20(1).png)

.avif)



.avif)
.avif)
.avif)
.avif)
%20(1).avif)

.avif)
.avif)


.avif)